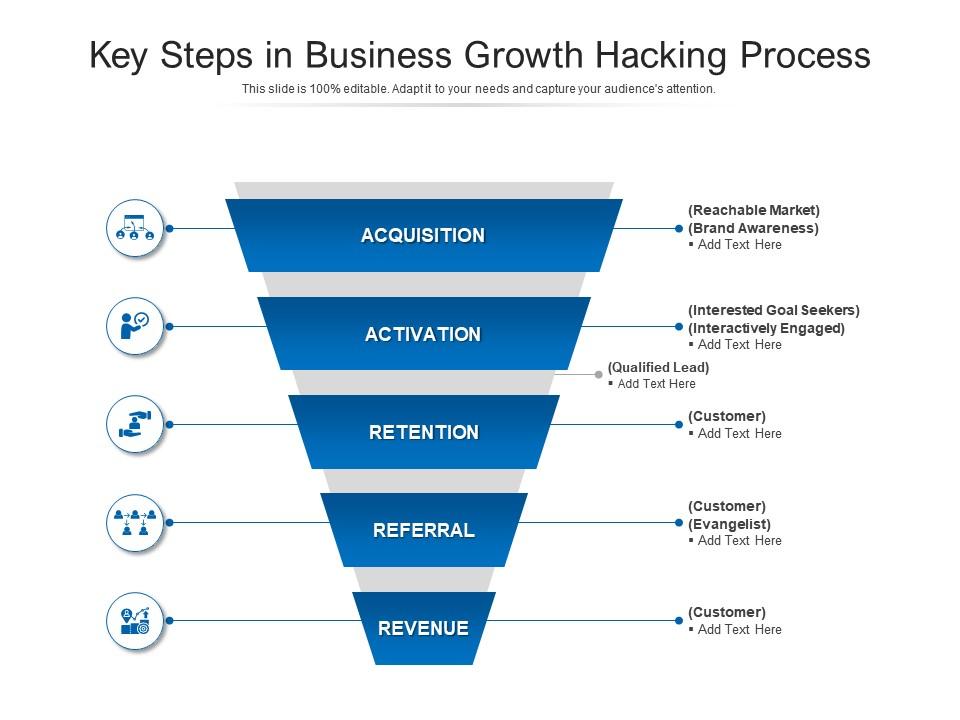
Key Steps In Business Growth Hacking Process | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

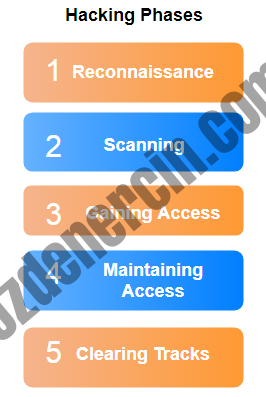
Hacker Combat™ on Twitter: "Five Phases Of Hacking #hacking #privacy #informationsecurity #cybersecurity #infosecurity #mondaythoughts #MondayVibes https://t.co/XhnP2PWprn" / Twitter

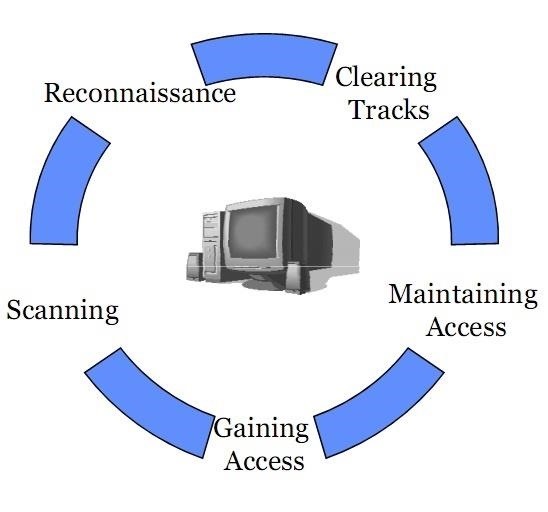
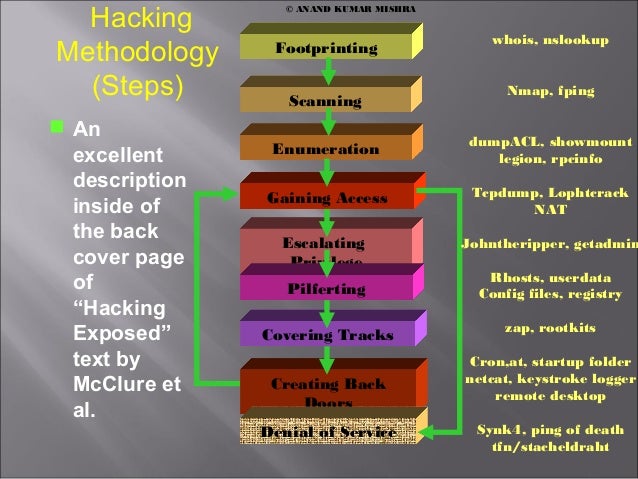
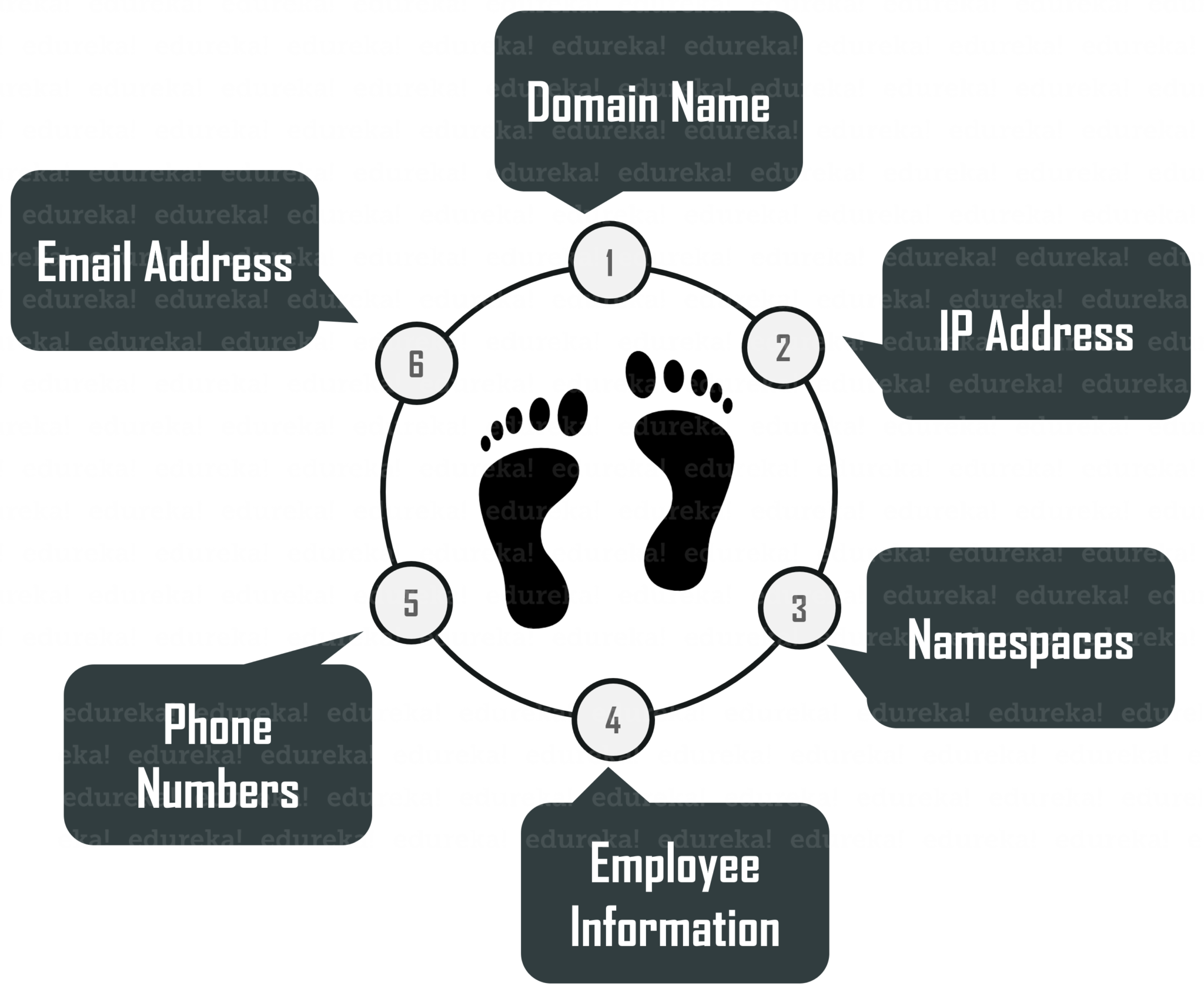
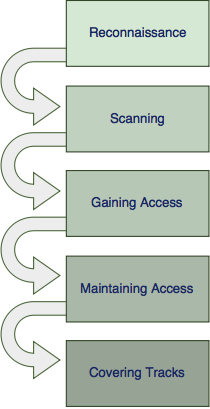
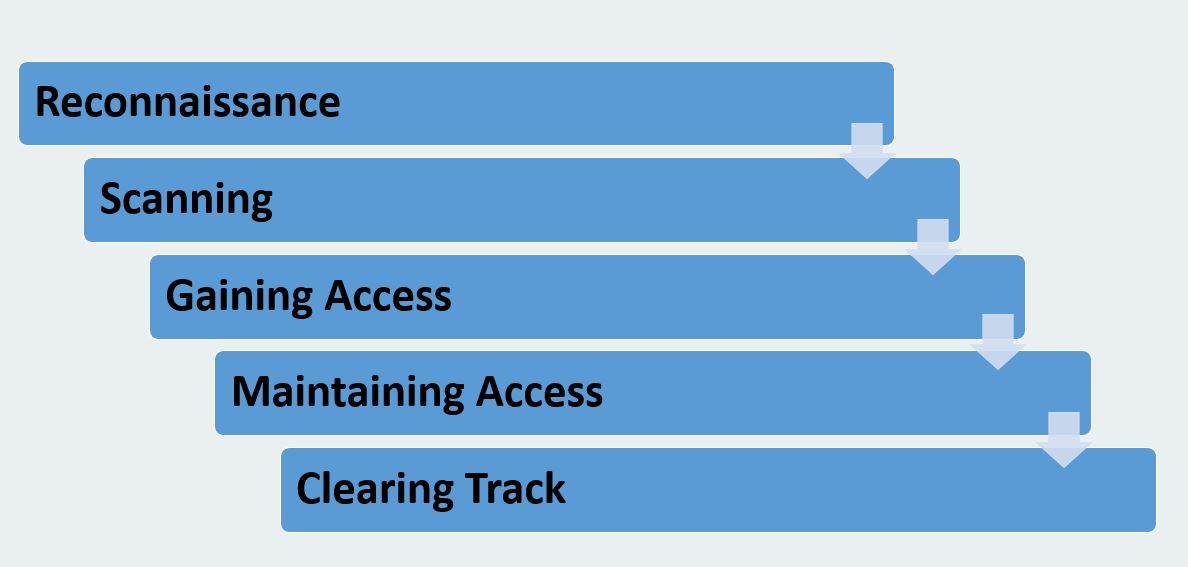
CEH Certified Ethical Hackers Society - Stages Of Ethical Hacking The below steps explain the different stages of hacking. Stage 1 - Reconnaissance: It is the act of gathering information related to